Quantum computing holds both a significant promise and a potential threat to the world of cryptography and cybersecurity. This dual nature lies in its capacity to vastly improve security measures, but also its potential to break existing encryption standards. Now, let’s delve into these aspects, starting with Quantum Key Distribution.
Quantum key distribution
Quantum Key Distribution (QKD) is a cutting-edge cryptographic procedure that allows the secure sharing of encryption keys between two parties. At the heart of this procedure is the sharing of encoded information across a quantum channel. Intriguingly, due to the intrinsic peculiarities of quantum mechanics, any attempted interception or measurement of the data triggers an irreversible transformation in its state. The recipients can detect this anomaly, thereby exposing the snoop.
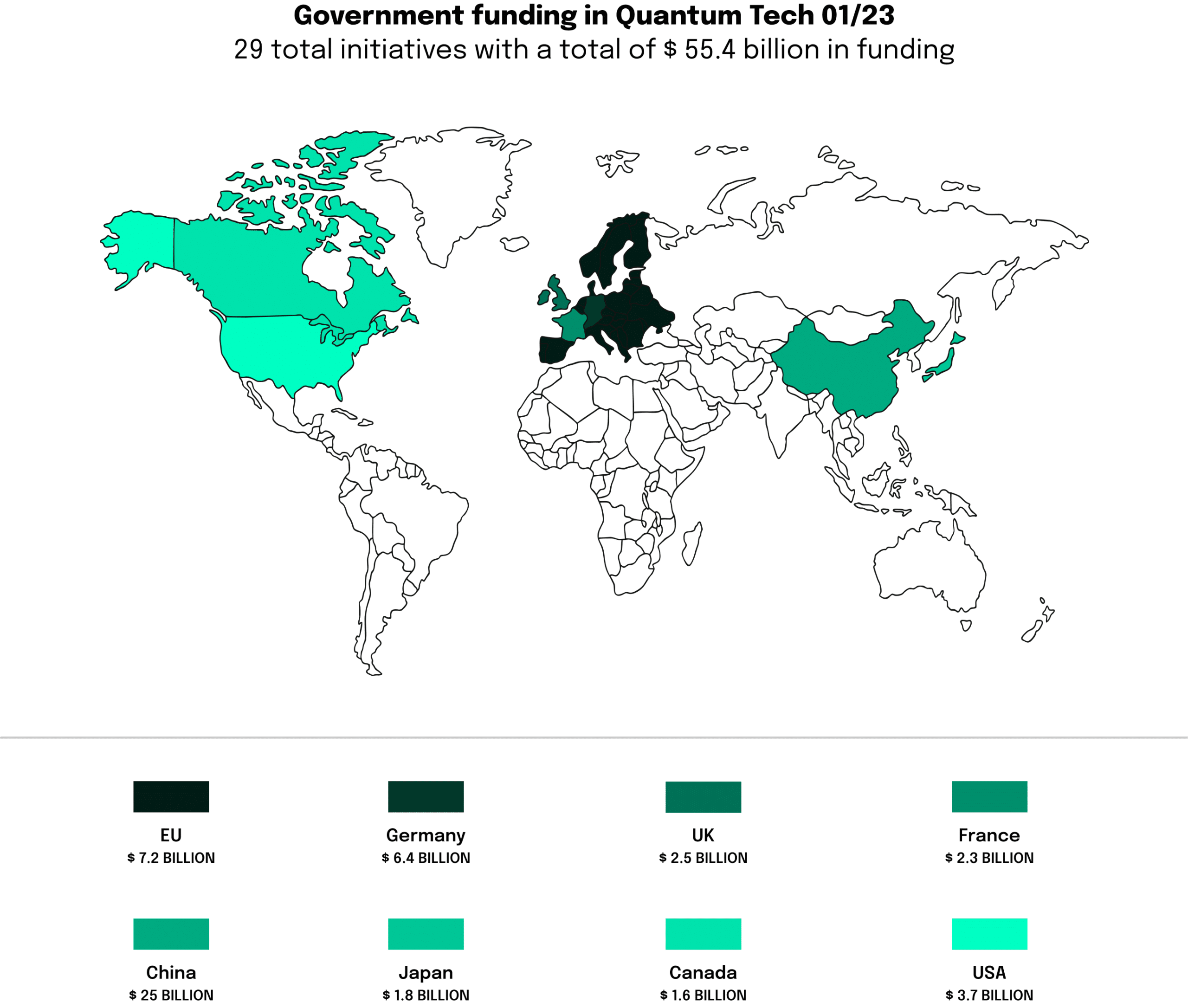
QKD’s defining characteristic is its theoretical invincibility against interception, making it a formidable weapon in the arsenal of next-generation cybersecurity. Several nations, China being a notable example, have begun utilizing QKD for safeguarding high-stakes communication channels, thereby showcasing the practical utility of quantum concepts in cryptography.
Breaking classical cryptography
Conversely, quantum computers are a looming storm cloud over classical cryptography. Algorithms devised for quantum computing, such as Shor’s algorithm, have the potential to decipher the widespread RSA encryption in polynomial time – a feat that poses an insurmountable challenge to classical computers. The fallout of this could be the exposure of a substantial volume of encrypted global data.
Modern encryption protocols, for instance, RSA and ECC, rest upon the computational difficulty of factoring large numbers or pinpointing discrete logarithms. Multiplying two numbers by each other can be solved with pencil and paper in any size. To decompose the same number into its prime factors, with today’s possibilities of mathematics, works in fact only by approximation and then trial and error. By efficiently factoring these numbers, Shor’s Algorithm could potentially break these encryption schemes.
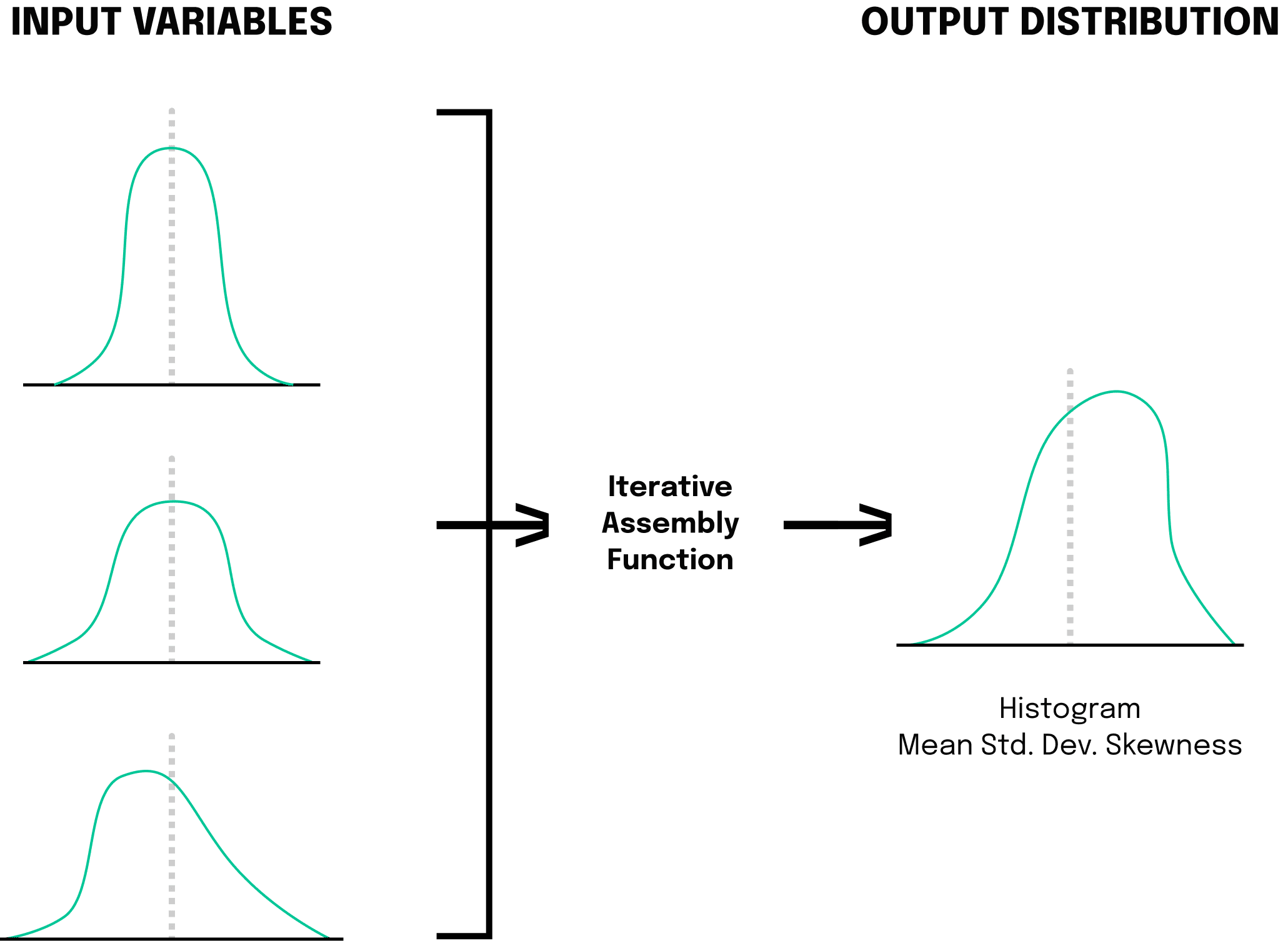
These tasks are a tall order for classical computers. However, quantum computers can accomplish these tasks efficiently, thereby casting a long shadow over current encryption practices. Consider a classical four-bit computer. Since classical bits can only be in one state at a time, these computers can only store 2^4=16 possibilities at the same time. That’s why it takes classical computers so long to divide numbers into prime factors as it is requested by RSA encryption. For a quantum computer other standards apply. A four qubits quantum computer, in superposition, is designed to be in all 16 possible combinations simultaneously. With this knowledge and Shor’s algorithm in mind, the quantum computer can store over one million values simultaneously (2^20 = 1,048,576). A big challenge for keeping information secure with classical methods.
This is not to suggest that the advent of quantum computers will lead to an overnight compromise of all security systems. The hardware prerequisites for running such algorithms on quantum computers are still far off. However, it is an alarm bell that signifies the urgent need for post-quantum cryptography.
On one side, quantum computing offers the promise of revolutionizing secure communication, courtesy of techniques like QKD. On the other, it poses a looming threat to existing encryption practices and underscores the urgency of evolving quantum-resistant algorithms. The discipline of cryptography is merely one among the plethora where the quantum revolution will usher in profound shifts, giving rise to novel opportunities and hurdles alike.